Too often, cyber str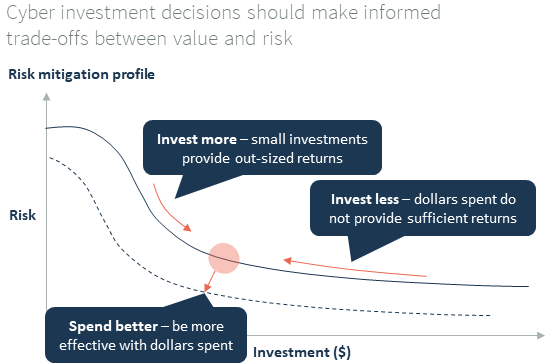 ategies focus on complying with best practices rather than on protecting ‘value’, with significant attention dedicated to Information Technology (IT). Meanwhile, Operations Technology (OT), the technology that runs your operations, is neglected. This is a clear signal that the cybersecurity plan did not start with a clear understanding of value, risk or cyber strategy.
ategies focus on complying with best practices rather than on protecting ‘value’, with significant attention dedicated to Information Technology (IT). Meanwhile, Operations Technology (OT), the technology that runs your operations, is neglected. This is a clear signal that the cybersecurity plan did not start with a clear understanding of value, risk or cyber strategy.
A sound cybersecurity strategy should start by understanding how critical each of your physical and data assets are, what cyber threats could compromise these assets and how likely this is to occur. This enables teams to develop mitigation plans and determine the associated value and costs. Without this value focus, many strategies are like spreading peanut butter on toast – evenly spread, rather than focussing on the at-risk assets.
When looking at your organisation’s cybersecurity strategy, it is crucial to rigorously review three questions:

 2. What is needed to protect our at-risk assets?
2. What is needed to protect our at-risk assets? 3. How do we know we are protecting our valuable assets effectively?
3. How do we know we are protecting our valuable assets effectively?Your organisation needs to understand how it delivers value, and what needs to be protected to realise that value and avoid incurring the expense of recovering from a cyber attack.
We offer pointers around the elements that should be covered by your cyber strategy:
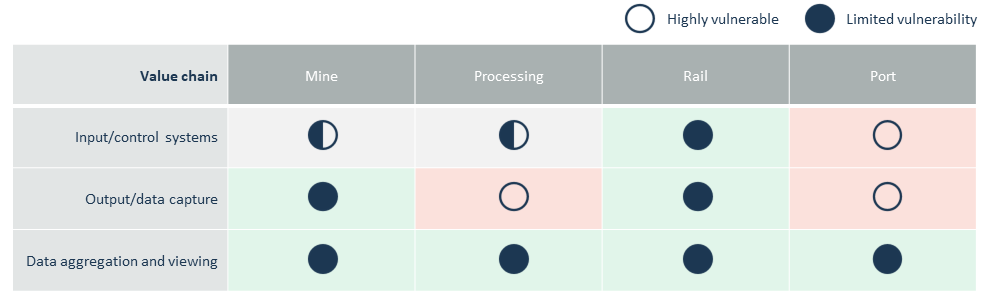
For each important asset, you can develop a view on whether it is at-risk by assessing both threat and vulnerability.
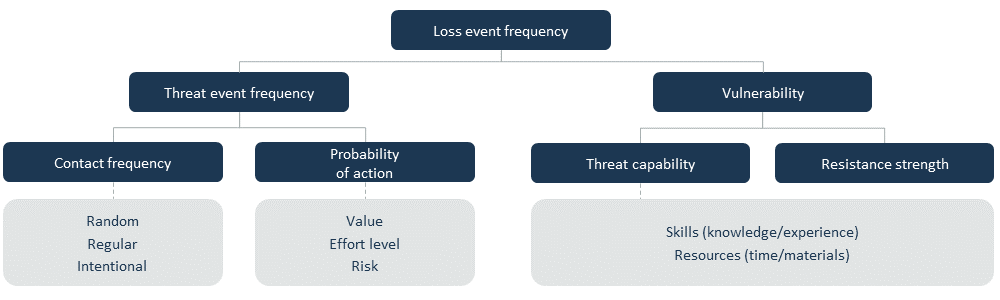
With an understanding of threats, capability and your current cybersecurity levels, Operations, Finance, Risk, and IT can work together and quantify your vulnerability and the financial risk of a successful cyber attack.
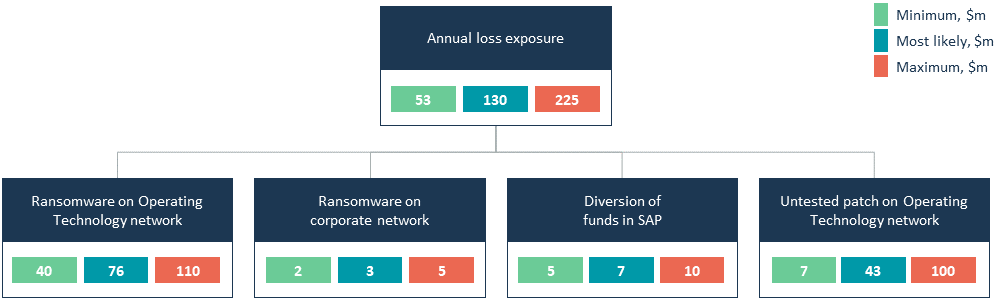
These analyses guide your technical teams in determining the required processes, systems and disciplines that need to be established within the organisation. This will include both technical and behavioural solutions, which trade-off potential mitigation value against both cost and ease of implementation.
These solutions can then be prioritised by the likely impact each idea or group of ideas will have on the magnitude of loss associated with that asset. Combined with the mitigation cost, this leads to further prioritisation based on the expected impact of mitigation strategies.
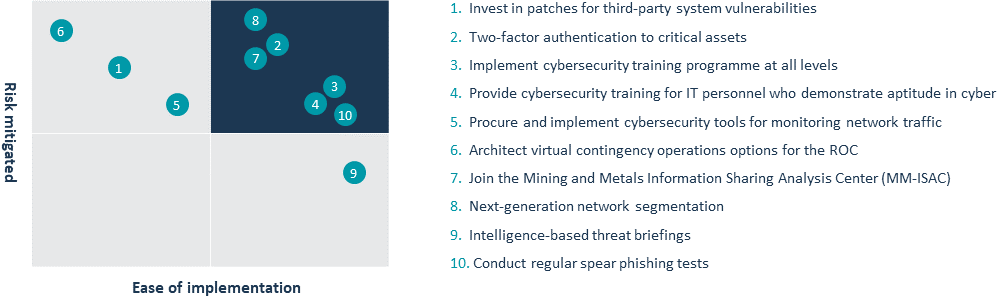
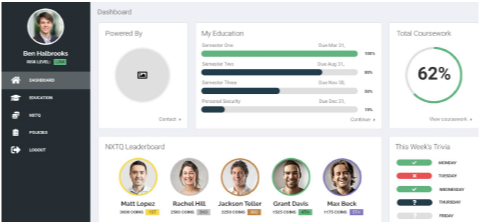
With a clear understanding of your vulnerabilities, risks and priority actions, your organisation can define a roadmap to cybersecurity. This will include a series of agreed initiatives and programs to improve your technical protection and resilience, while also training and coaching your entire organisation on how to stay cyber safe.
While cyber audits are useful to remain compliant with regulations and best practices, compliance alone does not deliver security, particularly when situations are rapidly evolving.
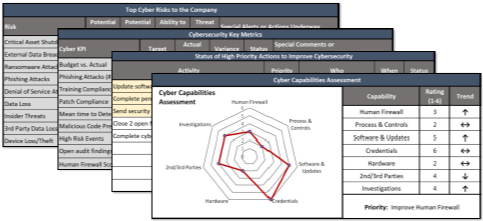
Your cyber strategy and execution should prioritise and protect the critical systems and data assets that power your operation. This will include tracking of actions required to position your organisation to defend critical assets, an overview of threats manifesting and any trends on how well the established defences are coping.
Unfortunately, common cyber KPIs often focus on ‘how dangerous it is out there’ (e.g. number of phishing emails received, number of external scans against the network), rather than whether the organisation is exposed or effectively protecting its at-risk assets. By shifting the focus of your KPIs (e.g. from ‘number of external scans against the network’ to ‘number of failed logins’), your organisation will gain a better understanding of potential target attacks, enabling it to act to protect itself. If you know that failed logins are increasing, you can identify which usernames and passwords may have been leaked outside the organisation, then focus efforts to increase security of those accounts and improve the training of those individuals affected.
Nothing can eliminate your cyber risk. However, a thoughtful, risk-informed and business-driven cyber strategy will enable your organisation to stay focussed on the priorities, make better decisions and focus funds on the most important areas to protect. You don’t need to be a cybersecurity expert to be an effective partner in the process, as your organisation moves beyond compliance and towards real security and value protection.
Key questions to ask:
Click to download a printable version of this article

Cyber Security Lead, Partners in Performance
Jason Israel leads our Australian cyber practice and is a former Pentagon cyber advisor and member of the Obama White House National Security Council.

Major General Patricia Frost, U.S. Army Retired, was the first Director of Cyber, Electronic Warfare, and Information Operations for the Department of the Army and has extensive cyber experience.
| We actively reduce the climate impact from our operations and invest in community-based climate solutions to balance remaining carbon emissions |